01
DEFINE YOUR
TRUSTED IPS
Add individual IPs or CIDR ranges to your allowlist. Single and office networks supported.
SCOPE: IP + CIDR
// module.hero.ip-whitelister
04
Staging environments, client previews, and internal tools should never be publicly accessible. IP Whitelister restricts WordPress access to approved IPs and CIDR ranges — without the lockout risk.
// CIDR SUPPORT · PROXY-AWARE · ADMIN LOCKOUT PROTECTION · CANTSTOP.DEV
// problem.statement
Staging sites, client previews, and internal tools are often accessible to anyone with the URL. Search engines index them. Clients stumble onto unfinished builds. Competitors find your work before launch. Without IP-level access control, your private environment isn't private.
STAGING VISIBILITY PUBLICLY ACCESSIBLE BY DEFAULT
CLIENT PREVIEW CONTROL NONE WITHOUT IP RESTRICTION
ADMIN EXPOSURE OPEN TO ANY IP THAT FINDS IT
┌──────────────────────────────────────┐ │ ACCESS LOG — UNPROTECTED SITE │ │ │ │ [09:14:02] 203.0.113.45 — GET / │ │ STATUS: 200 OK ← CLIENT? BOT? ? │ │ [09:14:08] 198.51.100.7 — GET / │ │ STATUS: 200 OK ← WHO IS THIS? │ │ [09:14:11] 192.0.2.88 — GET /wp- │ │ admin STATUS: 200 OK ← !!! │ │ [09:14:19] 203.0.113.45 — GET / │ │ staging/ STATUS: 200 OK │ │ │ │ AUTHORIZED VISITORS: UNKNOWN │ │ UNAUTHORIZED VISITORS: UNKNOWN │ │ CLIENT SAW UNFINISHED WORK: LIKELY │ └──────────────────────────────────────┘
// solution.introduced
IP Whitelister gives WordPress operators controlled perimeter access without the lockout anxiety. Define trusted IPs and CIDR ranges. Block everything else before it reaches sensitive content. Built-in admin safeguards ensure you can always recover access — even if a rule is misconfigured.
01
Add individual IPs or CIDR ranges to your allowlist. Single and office networks supported.
SCOPE: IP + CIDR
02
Non-approved traffic is blocked instantly and routed to your denied screen.
BLOCK: INSTANT
03
Admin bypass and lockout protection preserve recovery access for authorized operators.
SAFETY: BUILT-IN
┌─────────────────────────────────────────────────┐ │ ACCESS LOG — IP WHITELISTER ACTIVE │ │ │ │ [09:14:02] 203.0.113.45 — GET / │ │ IP CHECK: NOT ON ALLOWLIST │ │ STATUS: 403 BLOCKED → DENIED SCREEN │ │ │ │ [09:14:08] 10.0.0.45 — GET / │ │ IP CHECK: ✓ TRUSTED — OFFICE VPN │ │ STATUS: 200 OK → ACCESS GRANTED │ │ │ │ [09:14:11] 192.168.1.1 — GET /wp-admin │ │ IP CHECK: ✓ TRUSTED — ADMIN IP │ │ STATUS: 200 OK → ACCESS GRANTED │ │ │ │ UNAUTHORIZED VISITORS: 0 REACHED CONTENT │ └─────────────────────────────────────────────────┘
// module.specs
USE CASES
IMPLEMENTATION NOTES
// module.features
Lock down WordPress access with explicit IP and CIDR allowlists that keep restricted environments truly restricted — not just obscure.
SUPPORT .......... SINGLE IPS · CIDR RANGES · OFFICE/VPN NETWORKS
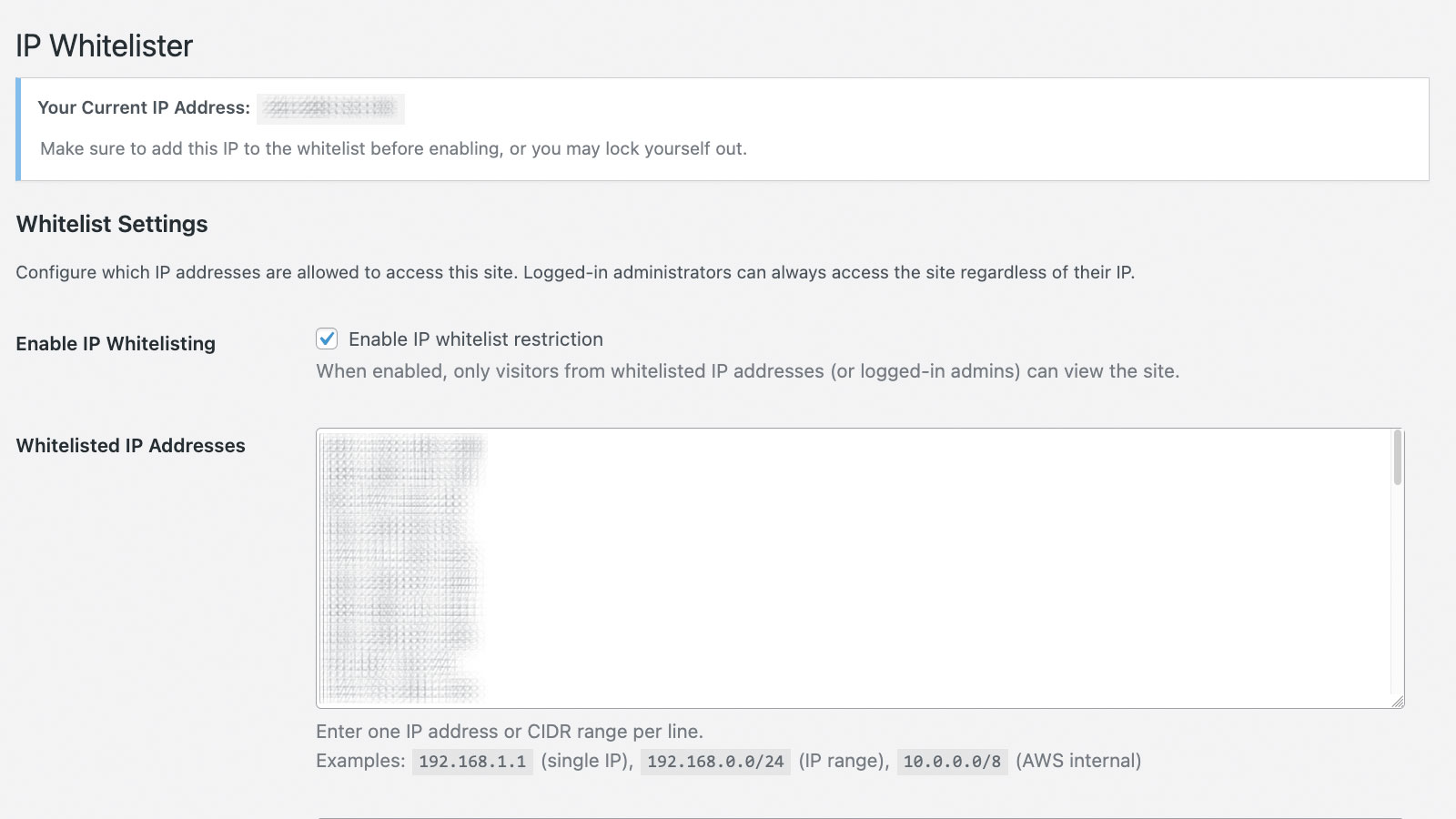
WHITELIST.SETTINGS.PANEL
Enforce stricter access policy with confidence — built-in safeguards reduce self-lockout risk so security improvements do not become operational emergencies.
LOCKOUT RISK .......... MITIGATED / RECOVERY PATHS PRESERVED
┌──────────────────────────────────────┐ │ LOCKOUT PROTECTION LOGIC │ │ │ │ RULE APPLIED: BLOCK ALL │ │ EXCEPT: [YOUR IP LIST] │ │ │ │ YOUR CURRENT IP: DETECTED ✓ │ │ ↓ │ │ ADMIN BYPASS: ACTIVE │ │ WP-LOGIN: PROTECTED NOT BLOCKED │ │ │ │ RESULT: RESTRICTIONS APPLY │ │ TO EVERYONE ELSE │ │ YOUR ACCESS: PRESERVED │ │ │ │ SELF-LOCKOUT RISK: MINIMIZED │ └──────────────────────────────────────┘
Control who can bypass restrictions and what blocked visitors see — so security policy stays strict while user experience stays clean.
UX CONTROLS .......... CUSTOM DENY MESSAGE · ROLE BYPASS · CLEAN BLOCK STATE
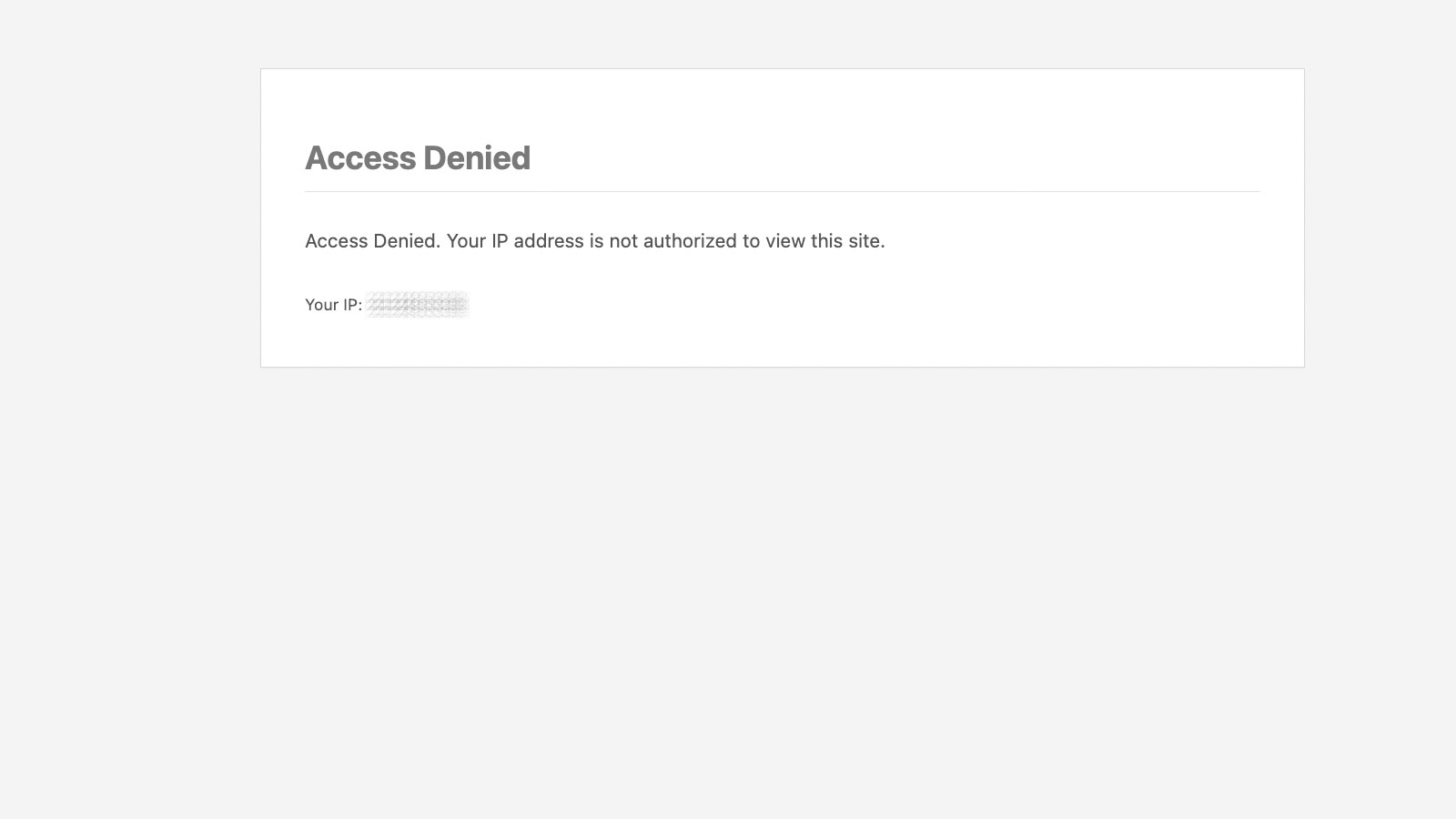
ACCESS.DENIED.EXPERIENCE
// module.showcase
IP Whitelister operates inside WordPress admin and delivers a clean denied-access experience for blocked visitors. No exposed error pages, no information leakage.
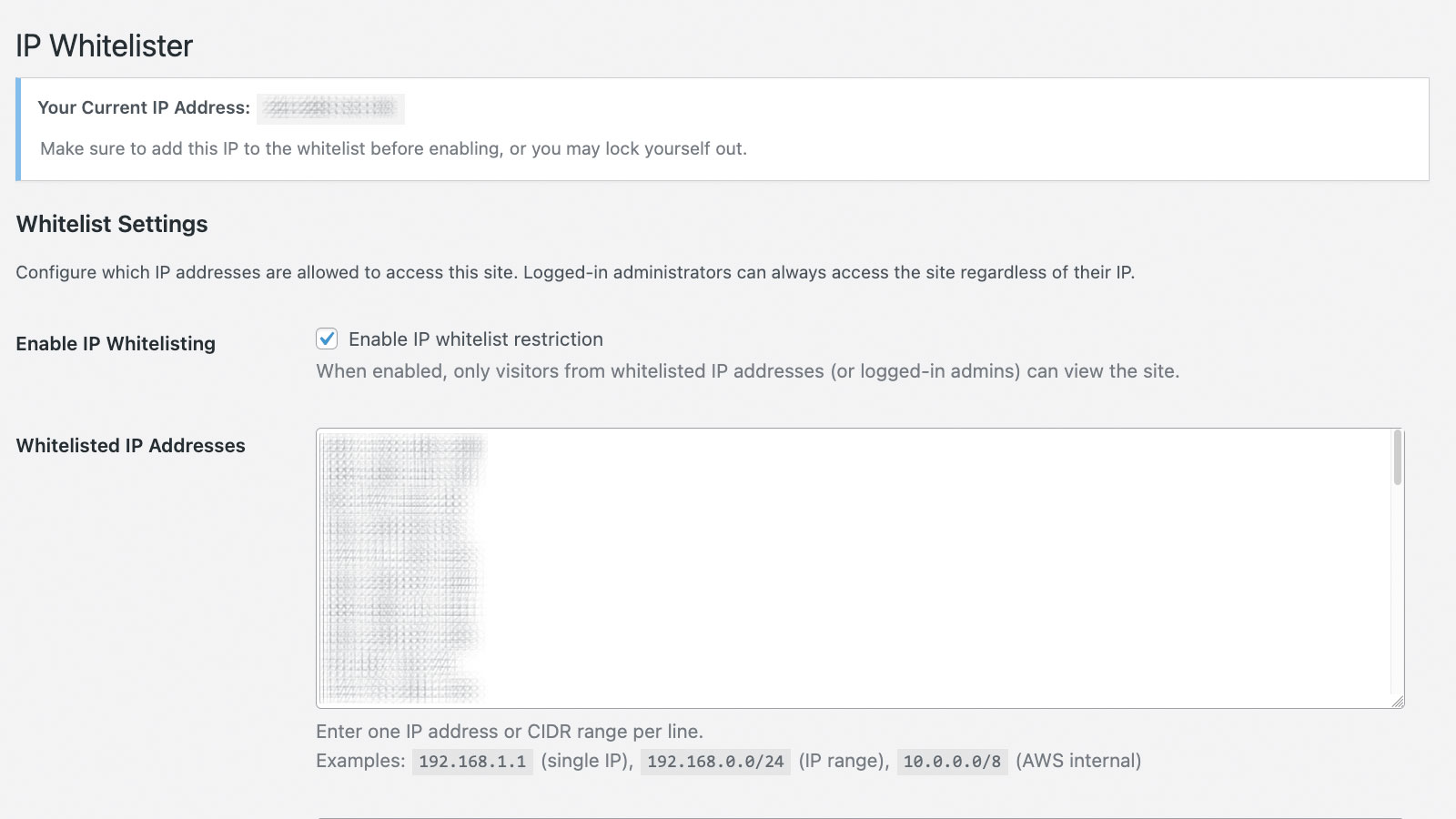 SCREEN.01
SCREEN.01
WHITELIST.SETTINGS.PANEL
Capture settings where IP and CIDR allowlist entries are configured and validated.
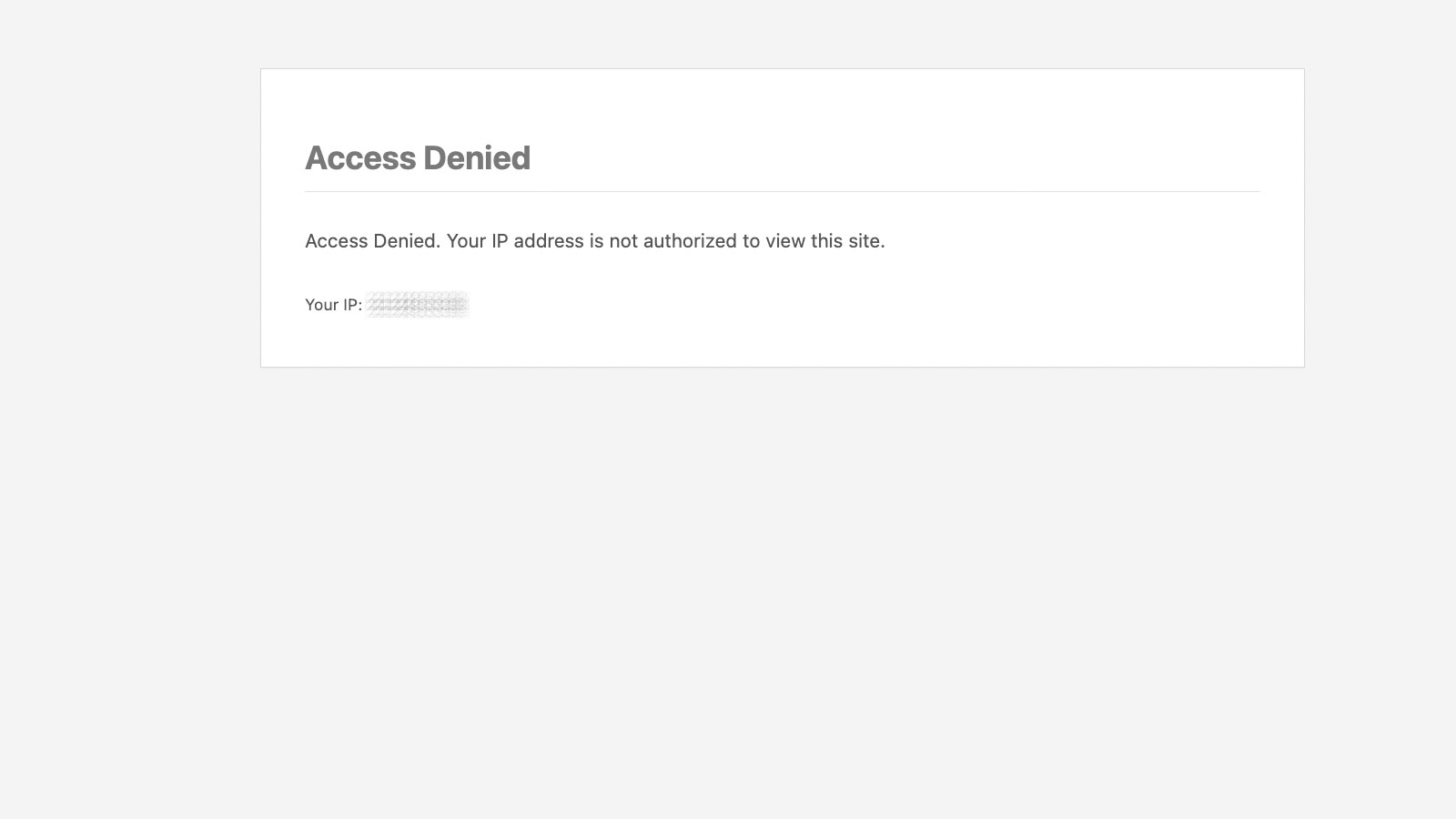 SCREEN.02
SCREEN.02
ACCESS.DENIED.EXPERIENCE
Capture the blocked visitor experience with the configured denial message.
// ip-whitelister · status check ────────────────────────────────────────────────────────── INCOMING IP ............. 203.0.113.45 CIDR MATCH CHECK ........ NO MATCH FOUND ROLE BYPASS ............. NOT APPLICABLE RESULT .................. ■ ACCESS DENIED DENY MESSAGE ............ CUSTOM / CONFIGURED ────────────────────────────────────────────────────────── INCOMING IP ............. 10.0.0.45 CIDR MATCH CHECK ........ ✓ MATCH: 10.0.0.0/8 RESULT .................. ✓ ACCESS GRANTED ──────────────────────────────────────────────────────────
// module.use-cases
[ USE CASE 01 ]
Building client sites on staging environments that must stay hidden until launch day — without relying on obscure URLs or server-level config.
WHAT THEY NEEDSTAGING LOCKDOWN
WHAT THEY GETIP-GATED ACCESS
ZERO SERVER CONFIG
[ USE CASE 02 ]
Managing client preview environments where only the client's office network should have access — not the public, not search engines, not competitors.
WHAT THEY NEEDCLIENT-ONLY PREVIEWS
WHAT THEY GETCIDR RANGE CONTROL
TRUSTED NETWORK BYPASS
[ USE CASE 03 ]
Running internal WordPress tools, intranets, or admin-only environments that should never be reachable from outside the office or VPN.
WHAT THEY NEEDPERIMETER CONTROL
WHAT THEY GETALLOWLIST ENFORCEMENT
PROXY-AWARE DETECTION
// module.pricing
At $9/year, IP Whitelister costs less than a single support call triggered by an exposed staging environment.
1 SITE
$9.00/YR
1 SITE LICENSE
BEST VALUE
2-5 SITES
$10.00/YR
UP TO 5 SITES
MOST POPULAR
6-10 SITES
$30.00/YR
UP TO 10 SITES
UNLIMITED
$50.00/YR
NO SITE LIMIT
// UNLIMITED TIER RECOMMENDED FOR AGENCIES MANAGING CLIENT SITES
ALL TIERS: YEARLY LICENSE · WP 6.0+ REQUIRED · INCLUDES UPDATES + SUPPORT · CANTSTOP.DEV
// module.faq
[ Q ]
IP Whitelister includes built-in admin lockout protection. It detects your current IP during configuration and preserves login and recovery pathways so you can always regain access — even if a rule is misconfigured.
[ Q ]
Yes. IP Whitelister is proxy-aware and evaluates trusted forwarding headers (like CF-Connecting-IP) to ensure allowlist decisions use the real client IP — not the CDN edge IP.
[ Q ]
Yes. CIDR notation is fully supported so you can allowlist ranges like 10.0.0.0/8 for an internal network or 203.0.113.0/24 for an office block — a single rule covers your whole team.
[ Q ]
A configurable denied-access page with a message you control. No exposed error codes, no server details, and no information that helps an attacker understand your environment.
[ Q ]
Yes. WordPress login and admin paths are covered by allowlist enforcement. Built-in admin bypass safeguards ensure authorized users do not lose access.
[ Q ]
Yes. Trusted roles can be configured to bypass allowlist enforcement — useful for internal workflows where certain users need access from variable IP addresses.
IP Whitelister restricts WordPress access to approved IPs and CIDR ranges. From $9/year.
YEARLY LICENSE · WP 6.0+ · CIDR SUPPORT · PROXY-AWARE · UPDATES INCLUDED · CANTSTOP.DEV
// module.cross-sell
[ COMPANY CARDS — $69/YR ]
Stored-value company purchase cards for WooCommerce checkout.
[ VIEW PLUGIN → ][ GOODINVOICES — $19/YR ]
Generate invoices and labels from WooCommerce in a single click.
[ VIEW PLUGIN → ][ ORDER SORT — FREE ]
Filter WooCommerce orders by product category. Free download, no license.
[ VIEW PLUGIN → ]IP WHITELISTER · PLUGIN · V1.0.0
FROM $9.00 / YEAR